CY(S)-5770 Software Vulnerabilities and Security (SoftVulnSec)
echo "Software Security" | sed s/\ /\ Vulnerabilities\ and\ /g
Instructor
For correspondence, send a mail to ek@ccs.neu.edu.
Office hours: Tuesdays, 2pm-3pm (send an email to get access to 177 Huntington)
Teaching Assistants
Naman Shah (shah.naman@northeastern.edu)
Lab hours: Tuesdays, Fridays, 4pm-6pm, RI 325
News
- 12.02.2025 Challenge 8 is online.
- 11.18.2025 Challenge 7 is online.
- 11.05.2025 Challenge 6 is online.
- 10.28.2025 Challenge 5 is online.
- 10.07.2025 Challenge 4 is online.
- 10.06.2025 Quiz 1 results are on Canvas.
- 09.29.2025 Challenge 3 is online.
- 09.22.2025 Challenge 2 is online.
- 09.18.2025 Final date announced. Check Canvas announcements for details.
- 09.15.2025 Challenge 1 is online.
- 09.11.2025 Account information has been sent and class Piazza has been setup
- 09.07.2025 The course website has been updated.
Abstract
Internet security has become part of everyday life where security problems impact practical aspects of our lives. Even though there is a considerable corpus of knowledge about tools and techniques to protect systems, information about what are the actual vulnerabilities and how they are exploited is not generally available. This situation hampers the effectiveness of security research and practice. Understanding the details of attacks is a prerequisite for the design and implementation of secure systems.
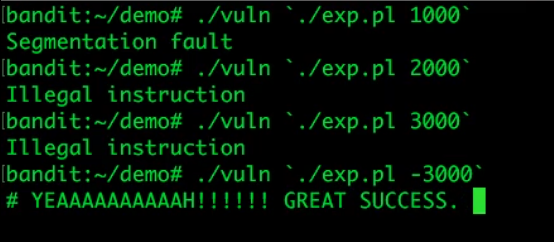
This course deals with common programming, configuration, and design mistakes and ways to detect and avoid them. Examples are used to highlight general error classes, such as stack and heap overflows. Possible protection and detection techniques are examined. The course includes a number of practical lab assignments where participants are required to apply their knowledge as well as a discussion of the current research in the field. Students will learn how the security of systems can be violated, and how such attacks can be detected and prevented.
The course aims to make the students "security aware", and gain an in-depth understanding about security issues.
Some Topics
- Operating system security and vulnerabilities
- - (UNIX, Windows, stack and heap overflows)
- Windows Security
- Memory corruption
- - (Buffer overflows, Heap overflows, Format string issues, etc.))
- Testing
- Reverse engineering and binary analysis
- Malicious code
- - (Viruses, Worms, Botnets, APTs, etc.)
- Language security
- Web security
Prerequisites
- Significant Programming experience
- - (This course is not for you if you are a beginner)
- Knowledge of C/C++ useful
- Basic SQL knowledge
- Basic web programming knowledge
Dates and Times
Mondays, 6-9pm, Hayden Hall 221
Slides, Material, and Schedule
All course materials will be available on Canvas.
- 12.08.2025 // Final
- 12.01.2025 // Class 11 // This will be a video (recorded) class
- 11.24.2025 // Class 10 // Slides are available on Canvas
- 11.17.2025 // Class 9 // Quiz 3 // Slides, demo videos are available on Canvas
- 11.10.2025 // Class 8 // Slides and demo videos are available on Canvas
- 11.03.2025 // Class 7 // Quiz 2 // Slides and demo videos are available on Canvas
- 10.27.2025 // Class 6 // Slides and demo videos are available on Canvas
- 10.20.2025 // Midterm
- 10.13.2025 // Indigenous People's Day, no class
- 10.06.2025 // Class 5 // Slides available on Canvas
- 09.29.2025 // Class 4 // Quiz 1 // Slides and demo videos available on Canvas
- 09.22.2025 // Class 3 // Slides and demo videos available on Canvas
- 09.15.2025 // Class 2 // Slides available on Canvas
- 09.08.2025 // Class 1 // Slides available on Canvas
Practical Challenges (Assignments)
Students will "need" to solve a set of practical challenges (assignments) in the lab part of the course. For more information on the challenges and the grading, check this page.
Grading
- 10%: 3 Quizzes
- 25%: Midterm exam
- 25%: Final exam
- 5%: Participation
- 35%: 8 practical security challenges
Registration
Registration details will be announced via e-mail to the registered participants.
Last Modified: Tue Dec 2 21:05:08 2025 EDT